Source: Bits And Splits via Shutterstock
Credential-stealing malware Vidar, which has lurked in the cybercriminal ecosystem since 2018, has vaulted to the top of the infostealer market following law enforcement takedowns of its two biggest rivals last year.
That shift was fueled by the malware author's calculated release of a major upgrade and expansion of Vidar's distribution network during the disruption, which positioned it as a go-to alternative for cybercriminals, according to new research from Intrinsec.
Rising to the Top
In a 43-page report, Intrinsec described Vidar as the most used infostealer on Russian Market, a cybercrime marketplace, since November 2025. It has displaced both Lumma and Rhadamanthys after law enforcement disrupted those previously top ranked infostealer operations in May 2025 and November 2025, respectively.
The shift is significant because Vidar is a high-volume, broad-spectrum credential harvester that some high-profile threat groups, including Scattered Spider, have used in their campaigns. The growing client base means more threat actors are now deploying the malware against corporate networks.
Related:Unpatched 'PhantomRPC' Flaw in Windows Enables Privilege Escalation
"Chaos is a ladder and Vidar successfully profited of the instability resulting from the takedowns of Lumma and Rhadamanthys, to rise to the top of the infostealer ecosystem," the French cybersecurity firm said in its report. "Due to the high volume of sample[s] and indiscriminate campaigns targeting users worldwide, we can expect to continue seeing several compromise attempts against corporate networks using this malware."
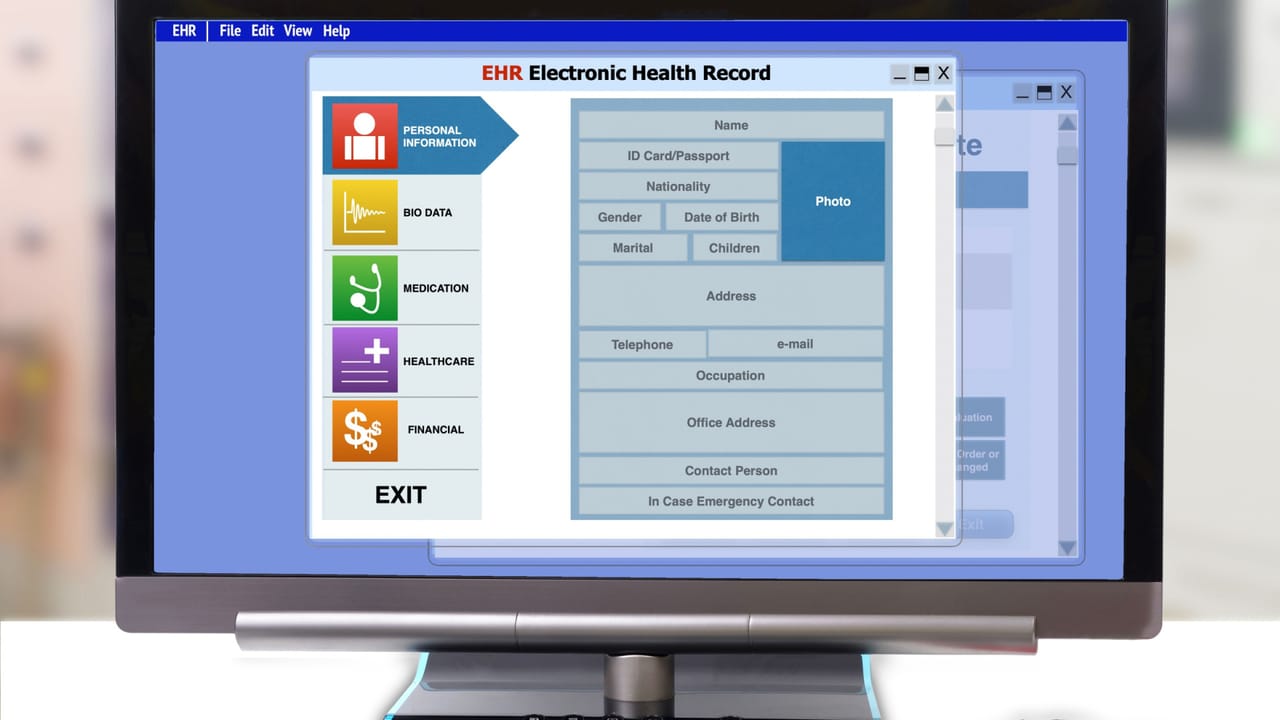
Like most prolific infostealers, Vidar targets a wide array of sensitive data that threat actors can use in future attacks against organizations. The malware pulls saved passwords, cookies, autofill data, and session tokens from major browsers including Chrome, Firefox, Edge, Opera, Vivaldi, Waterfox, and Palemoon.
Cryptocurrency wallets are another focus, with Vidar's operators hosting a curated list of cryptocurrency wallet browser extension IDs on their own infrastructure. The malware can also capture screenshots, harvest email client data, and exfiltrate local files to give attackers a comprehensive picture of a victim environment.
Stolen credentials, according to Intrinsec, are quickly monetized on underground marketplaces like Russian Market. Adversaries typically have used such credentials to take over accounts, move laterally inside a network, deploy ransomware, escalate privileges, and execute other malicious actions under the guise of a legitimate user or service.
Related:Bad Memories Still Haunt AI Agents
Distribution Tactics
Attackers are using a variety of methods to distribute Vidar. The most common tactics include phishing attachments disguised as legitimate software installers from file-sharing platforms, and social engineering lures on YouTube that redirect users through popular file-sharing services to malicious downloads. Other researchers have documented attackers using ClickFix campaigns, Trojanized npm packages, and fake game cheats to deliver Vidar.
One significant contributor to Vidar's recent growth, according to Intrinsec, has been the decision by its operators to collaborate with so-called "Cloud" channels on Telegram, which are public or semi-public channels where cybercriminals freely share stolen credential logs. These channels, going by names like Kata Cloud, Poltergeist Cloud, Cron Cloud and Omega Cloud, have helped advertise Vidar and attract more clients to the malware, Intrinsec said.
"Telegram 'cloud' channels fuels the ecosystem of stolen logs and help advertise the stealers behind the stolen data," the security vendor said. "Subscribers to these channels may notice that more channels are now using Vidar and therefore think that this is a useful program to steal data."
Vidar's infrastructure is designed to survive takedown attempts. One mechanism that Vidar's operators have used to try and hide its command-and-communications (C2) systems is "dead drop resolvers," which is a technique where the malware doesn't directly include its C2 address. Instead, the malware contains URLs pointing to legitimate public platforms such as Telegram, where attackers embed the actual C2 address in a profile description, a post, or an account bio. When Vidar lands on a victim system it reaches out to these URLs to retrieve the real C2 details dynamically, thereby evading static detection and blocking, Intrinsec said.
Related:Google Fixes Critical RCE Flaw in AI-Based 'Antigravity' Tool
Intrinsec's recommendations for protecting against Vidar include enabling multifactor authentication for browser-related accounts to mitigate credential theft, deploying DNS filtering and secure Web gateways to block known malicious domains and IP addresses, and using sandbox solutions to analyze email attachments and URLs.


.jpg)






.jpeg)
